The Ultimate Guide to Accessing Geo-Restricted Social Media Content

Are you tired of being blocked by a site on the internet because it’s unavailable in your country? Many people from around the world experience this dilemma due to geo-restricted material.
“Geo-restricted content” is any online material or website that is not accessible in the country where the user is physically located, moreover some countries require that the website hosting server be located within its borders like China, Russia, and other locations for better control or even the ability to seize the servers if they wish to. These restricted platforms may include movies, e-commerce websites, or social media platforms like Instagram, Facebook, or Twitter.
The good news is that using 1clickvpn to connect your device to an external server via the internet can help you bypass these restrictions. Private networks have been growing in popularity worldwide, as they can have a host of benefits. One key feature is that they allow people to unlock content that was previously behind a wall.
In the United States, for example, VPNs reached an 88 percent awareness rate in 2022, with seven out of ten citizens using a private network for either work or personal reasons.
We’re going to give you the juicy details on how you can begin using programs to access various social media content despite geo-restrictions.
How do VPNs Function?
Whenever you are restricted to websites or region-specific content, a VPN acts similarly to a “proxy.” By connecting your device to an external computer, or “server,” a private program hides your IP address and lets you use the server’s web connection instead of your own when browsing online.
Simply put, when connected to a server location, it may appear you’ve been based in that country yourself! All network traffic passes through this virtual network created by the VPN, making it simple to get around web restrictions and enable remote access.
How Does Geo-Restriction Work?
Whenever you visit a website, your device sends a connection request. This request includes your precise geographical location.
If your country is banned, you will be taken to a page that says “content not available in your country.” Alternatively, you can be directed to the content you want to access if your region is on a list of “whitelisted” regions.
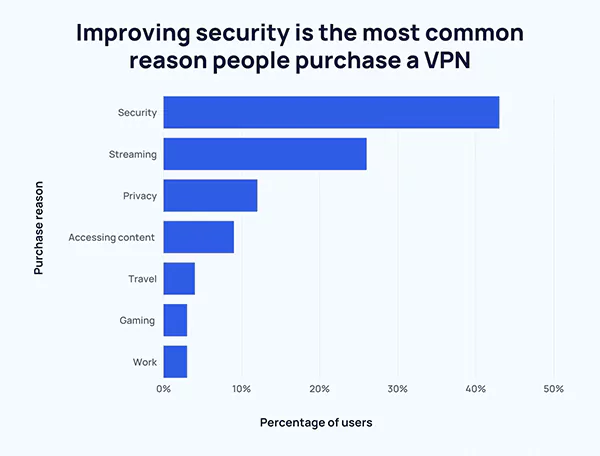
This graph shows the reasons people purchase a VPN membership. You can see that security is the biggest reason why people go for these programs followed by streaming.
Bypassing Geo-Restrictions with VPNs
If it appears fair or not, social media companies use geographical restrictions when determining which content users access on their platforms. This system may seem reasonable on paper; however, it does lead to many people being locked out of relevant information or entertainment because of their location.
Fortunately, virtual private networks have found a way around such restrictions by allowing users to connect through different servers based globally.
Users don’t need technical expertise; they merely choose the country they would like to appear as coming from by connecting through a VPN server located there—USA for UK content, Japan for US content, et cetera!
In social media situations, many view TikToks as a potentially banned social media site—with a VPN. However, you maintain your freedom to use the popular social media channel, which could be particularly significant if you are a social media marketer.
Not only that, but private networks also offer substantial user data protection since all transmitted data is encrypted, which keeps hackers away from accessing user information or tracking their online activity.
It is also good to make a mental note that if there are circumstances in which your current network is being blocked and causing frustration accessing content online, you shouldn’t become hopeless, as there is always a way to troubleshoot it! Just try changing the servers and see which ones you can access.
If trying several servers doesn’t work, consider switching entirely to another provider who can provide better solutions for your needs.
Choosing the Best VPN
Finding the best VPN provider for you can be a long and boring task because there are so many options. However, there are some factors to consider while picking, such as the availability of server locations, the strength of the internet connection, and how they handle client data confidentiality issues.
The major factor here is reliability; only select a provider with a good record that guarantees secure connections through solid encryption protocols and has server networks positioned precisely where required most.
How to Begin Using a VPN
Setting up a VPN is relatively straightforward. First, choose a trustworthy provider and install their program on your device. After establishing a connection with the server to which you desire access, you are free to browse!
It’s noteworthy that when implementing a service provider, it’s inevitable that connectivity speeds can fluctuate significantly based on various factors, such as platform detection systems. This makes going for dependable vendors who provide fast connections necessary for an optimal experience with low latency.
Moreover, specific countries or institutions prohibit using Virtual Private Networks; therefore, one should conduct some research before usage.
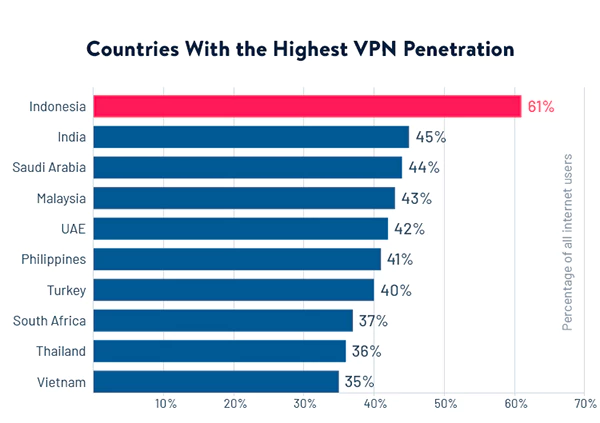
These are the countries with the highest VPN penetration. Indonesia leads the list, whereas countries like India, Saudi Arabia, Malaysia, and UAE come next.
Best VPN Usage Practices
Be aware that some platforms can still see through virtual private networks; hence, it’s paramount to always pick credible providers during the time you take extra precautions to safeguard privacy and security online, all when avoiding free services as they collect data for third-party advertisers.
Investing in a top-notch VPN service is advised to guarantee complete anonymity during the time you browse the internet. You can feel secure knowing that private information or online activities are kept strictly private by choosing a paid subscription that ensures trustworthy encryption and a no-logging policy.
CooMeet: Your Ultimate Video Chat Destination
Leveraging Social Media for Networking and Job Search:…
How to Stay Safe on Your Social Media…
Mastering the Digital Domain: 5 Social Media Marketing…
Why Ghost Trails Feature Disappeared: Did Snapchat Remove…
Understanding Why Don’t I Have Instagram Notes &…
How to Change Age on TikTok? An Ultimate…
Instagram Profile Viewer: Can You See Who Views…
Learn 15+ Easy Ways to Fix Instagram Keep…
TikTok Watch History: An Ultimate Guide on How…
The Ultimate 2024 Guide to Instagram Story Size…
All You Need to Know About TikTok’s Viral…