The 5 Best Practices for HIPAA Compliance
Introduction
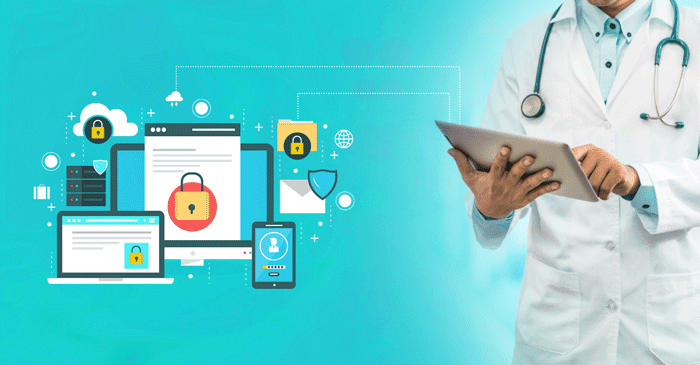
All healthcare practitioners and their business associates are required by US law to abide by the rules outlined in the Health Insurance Portability and Accountability Act (HIPAA). HIPAA regulations provide rules for the electronic exchange of patient data and secure medical records while preventing fraud. HIPAA compliance is a daunting notion, especially given that, depending on how severe the offense was, non-compliance penalties might result in fines of up to $250,000. Most of the time, it serves businesses’ best interests to hire or train a HIPAA compliance specialist committed to ensuring security regulations are followed and keeping an eye on how staff members handle patient information (patient-protected healthcare information).
Best Practices for HIPAA Compliance
HIPAA compliance involves more than just utilizing the right technology. It is equally important to put good rules and regulations into practice. Here are some crucial recommendations to make sure your clinic complies with HIPAA regulations.
Identification and Access Control
Access controls are an excellent example of how technology is essential to enhancing data flow. Owners, managers, and custodians should be included in accessing protected EPHI. Although there are no technical standards, any firm that wishes to comply with HIPAA is advised to use access management and identification systems. Without this technology, managing access and the data related to approvals, requests, and denials would be tough. Automating the essential account privilege recertification is another way technology may help.
Document Destruction
The identity thieves have been identified for searching trash bags outside companies for sensitive information. To ensure that documents are destroyed before they leave your safe locations, ensure you have many excellent shredders. It is insufficient to have a box full of papers that will be destroyed later. When superfluous records are identified, they must be destroyed.
Employing Staff
One of the simplest ways to maintain training a top priority is to focus on compliance. All staff should get continuous, current training on managing PHI, including instruction on cybersecurity. Make a plan for training that explains the regulations and how they apply to each employee’s position. All employees should get instruction on HIPAA rules and procedures, PHI usage, and disclosure throughout the hiring process and annually after that.
Review of Information System Activity
Techniques for reviewing the information system’s activity logs include access logs, audit logs, and reports on security incidents. However, before doing all that, businesses must adhere to best practices to take control of the protected information they hold and use common sense to manage access to that information.
Encryption of Data
Theft or loss of mobile devices that store encrypted data and the transfer of unencrypted ePHI across open networks are the leading causes of ePHI security breaches. When all ePHI is safeguarded, these types of breaches can be readily averted. Although HIPAA regulations do not currently mandate encryption in all circumstances, it is nevertheless an essential security measure that needs to be carefully considered and addressed. If data encryption is not employed, relevant alternatives should be considered. Data encryption prevents unauthorized access to stored data and makes stolen data useless. Patient data will not result in a HIPAA violation if an encrypted device is stolen or lost because it will not be disclosed. Data encryption is crucial to preventing hackers from accessing your data on computers.
Conclusion
Clinics, hospitals, and other healthcare organizations handling patient information must adhere to stringent regulations to guarantee data security. Both the public and commercial sectors may implement the policies. Compliancy Group is the most well-known HIPAA compliance software to assist you in achieving HIPAA compliance. The best practices covered in this article can ensure that your data is not stolen or compromised and that your business is not subject to harsh fines for breaking the law.
Fitness Technology: The Latest Updates and Implications for…
Exploring Telemedicine Credentialing: Tips and Considerations
How to Keep Your Fitness Routine on Track…
The Ultimate Guide for Picking the Perfect Medical…
Take Care & Worry-Less with Bajaj Finserv Health…
LIS vs. LIMS: What’s The Difference?
Know About Various Types of Hair Transplantation
Top Workout Accessories of This Season
How to Develop High-Quality Medical Image Analysis Software
How Healthcare Industry Leverages Machine Learning Through Wearables
5 Best Aromatherapy Diffusers to Buy Online in…
Why are Blue Light Glasses Trending?